Top User's Choice
iDeals Virtual Data Room
Intro
Banking-grade security, excellent support, ease of use, and intuitive interface — these are four pillars of a great virtual data room. And this is what iDeals is best known for.
iDeals has an industry leading 99.95% uptime and offers 100+ features for secure document sharing and collaboration. The platform supports 25+ file formats and 15 languages, making it a versatile option for businesses of all sizes, from startups to large enterprises, across various industries including IT, finance, law, technology, real estate, energy, manufacturing, insurance, and healthcare.
The company’s global presence, with headquarters in London and ten additional offices around the world, further underscores its commitment to serving customers on a global scale.
Since its foundation in 2008, iDeals has been consistently recognized with multiple awards. The company has won the past 15 G2 Market Leader awards, including the latest Winter 2023 Leader, consolidating its reputation as the market’s most user-friendly data room, according to customers’ reviews.
Read the detailed review to learn why iDeals is one of the top choices for dealmakers looking for a reliable virtual data room.
Product Screenshots
Contact Details
Year Founded 2008
Website www.ideals.com
Product Overview
iDeals is a modern, yet experienced company developing customer-oriented solutions.
Their virtual data room aims at making customers’ businesses more efficient and profitable. This business-oriented attitude starts with the company’s mission — “creating more prosperity in the world by accelerating high-stake business decisions.”
With a commitment to providing exceptional customer support and bank-grade security, iDeals offers an intuitive and user-friendly interface that is easy and fast to set up, making it a favorite among users with varying levels of technical expertise.
Not only is iDeals committed to providing a user-friendly experience, but the company also offers a virtual data room interface in 15 different languages, making it accessible to a wider audience.
Additionally, iDeals warmly welcomes new users and provides them with a free 30-day trial to explore the platform.
As per the support, all incoming calls are answered within 25 seconds, and issues are solved within 5 minutes.
When it comes to data security, iDeals takes it as a top priority. Among the variety of security measures, they offer 8 levels of access permissions, which means absolute control on who can access what and when, ensuring that confidential information is kept private. Besides, iDeals uses multiple certified data centers that guarantee physical security of users’ data.
According to online reviews, iDeals virtual data room is a favorite clients’ choice for conducting complex transactions such as M&A, especially for the due diligence process. This is what some of iDeals customers’ reviews say about it:
“All functions that we are looking in a data room are available (organizing documents, managing accesses, etc.), but the ability to generate reports and also to redact documents directly in the data room are two functions that I like best. There is really nothing that I dislike that I can think of.” — Caroline M., President and Managing Partner.
“When doing diligence with external parties, iDeals is such a great tool to be organized and professional. It is easy to navigate and when you have issues, their customer service team is 2nd to none!” — Angela T., Executive Assistant.
Users also indicate that iDeals makes due diligence smooth and effective due to the straightforward in-built Q&A workflow and multiple automations such as indexing.
They enjoy that they can easily post questions, assign experts inside the platform, and get tailor-made prompt notifications letting them know about new responses. Additionally, users praise the ability to attach documents in response to questions, which makes collaboration between all parties straightforward.
iDeals customers especially like the detailed reports on users’ activity inside the data room on a page-by-page basis and automatic e-mail notifications that inform about each activity. With these features, they always know what potential investors are most interested in and can react proactively, accelerating the deal.
iDeals Virtual Data Room Product Details
Average Users' Ratings
Provider's Features Rating
Data was gathered from our users' reviews and data from G2 and Capterra.
iDeals data room pricing
iDeals has a subscription-based pricing model — three subscription plans created to serve different needs:
- Pro — for small and mid-sized projects
- Business — for large projects and serial dealmakers
- Enterprise — for larger enterprises with various business objectives
All subscription plans include:
- Two-factor authentication
- Remote shred
- Detailed audit trails and reports
- SOC 1/2/3 and ISO 27001:2013 certified data centers
Every subscription plan is based on the number of users, admins, and projects allowed as well as available storage capacity.
| Projects | Admins | Storage | Users | |
|---|---|---|---|---|
| Pro | 1 | 5 | Up to 10 GB | Unlimited |
| Business | Unlimited | Unlimited | Up to 250 GB | Unlimited |
| Enterprise | Unlimited | Unlimited | Up to 1 TB | Unlimited |
Benefits of the iDeals data room
Below are the main advantages of using iDeals virtual data room:
- Banking-grade security. iDeals takes serious measures and offers a variety of security features to provide their customers’ confidential data with high-level protection.
- Ability to fully customize your VDR. Add your company’s branding look and feel to the VDR as well as customize invitation emails, watermarks, and terms of access.
- Easy and fast deployment that takes 15 minutes in average. iDeals is easy and fast to set up and use, regardless of the user’s technical background or project size.
- Advanced Q&A workflow. Users can initiate discussions and post questions to experts inside the virtual data room, which significantly improves collaboration on the project.
- Plugin-free IRM protection. It enables document encryption on opening or downloading access to the file without any extra plugin.
- Auto-notifications. It allows users to get prompt notifications when certain actions are taken on documents in the data room.
- Single Sign-On integration. It allows users to quickly enter different projects in the data room via a single corporate login.
- Granular page-by-page reporting. It provides admins with detailed reports on what actions were performed on a particular document on a page-by-page basis.
- Industry-leading 99.95% uptime. iDeals delivers a highly secure and resilient environment with 99.95% uptime thanks to the redundant design of infrastructure.
- 8 levels of access permissions. Admins can set certain access permissions for each user, limiting their access to files as needed.
Features of iDeals
Security features
iDeals considers customers’ data security a top priority and, therefore, offers a variety of security features. These can be divided into three groups — document security, access security, and security compliance.
Document security
- Dynamic watermarking. It enables automatic personally-identifiable marks to appear on top of every document when it’s viewed, downloaded, or printed.
- Fence view. The viewer can only see the part of the document where the cursor hovers, while the rest of the document is masked by a digital fence.
- Redaction. The highly confidential parts of the document are hidden (blacked out) for the viewer.
- Secure spreadsheet viewer. It allows the secure viewing and editing of Excel files online.
- Granular document permissions. There are 8 levels of document access rights: None, Fence View, View, Download Encrypted PDF, Print, Download PDF, Download Original, and Upload.
- Plugin-free IRM. It enables document encryption on opening or downloading access to the file.
- Remote shred. Admin can set how long files are available for viewing or downloading and can revoke access rights to files even after downloading.
- Remote wipe. It allows remote locking and wiping of encrypted data from lost or stolen devices.
Access security
- Time and IP access restriction. Admins can restrict access from certain IPs or set accessible periods.
- Two-factor authentication. Virtual data room visitors need to undergo two-step identity verification — through a password and single-use SMS code.
- Granular user permissions. Admins have the option to restrict or provide access rights to users or user groups, including view, secure PDF download, print, download original, and edit.
- User security impersonation. It allows admins to view files from the particular user’s perspective to make sure they can only access the documents they need.
- Access control and expiration. It allows for customizing policies on password strength and duration of the user session and setting expiration dates for file access.
- Mobile device management. It implies controlling the accessibility of secure documents on mobile devices.
Security compliance
- 256-bit encryption and 2048-bit keys at rest and in transit. This is one of the most secure encryption methods that’s used in most modern encryption protocols and technologies, such as SSL and AES.
- GDPR compliance. This is the toughest privacy and security law in the world that’s relevant to the European Union and European Economic Area. However, it imposes obligations to companies around the world as long as they target the data related to people in the EU.
- HIPAA compliance. Health Insurance Portability and Accountability Act of 1996 (HIPAA) protects the security and confidentiality of the healthcare-related information shared via the iDeals VDR.
- ISO/IEC 27001:2013 certification. This certification speaks about iDeals addressing information security in three dimensions: integrity, confidentiality, and availability.
- SOC 1/2/3 certification. iDeals strictly follows the SOC security standards, including risk management, communication, physical data access, system operations, control monitoring, and change management.
- CCPA compliance. California Consumer Privacy Act targets privacy rights and consumer protection for the residents of California, United States.
- LGPD compliance. This compliance proves that iDeals has earned client confidence in managing data privacy of clients in Brazil.
- OWASP compliance. OWASP is a non-profit organization that’s dedicated to improving software security.
- SDL compliance. It speaks about data security through all the phases of the software development process.
Interface features
iDeals’ customers often boast how much they enjoy its modern and easy-to-navigate interface. Below are the most popular features:
- 15-minute setup. An iDeals virtual data room is easy and fast to set up — 15 minutes, and you’re good to go.
- Multilingual interface. You can access iDeals in any of the 14 languages available, including English, German, French, Spanish, Polish, Turkish, Japanese, Chinese, and Korean.
- Application for desktop and mobile. iDeals has a desktop application for Windows and mobile applications for iOS and Android.
- Seamless cloud/desktop synchronization. All the changes you apply to a virtual data room in the cloud will be instantly synchronized with the desktop application.
- Scroll-through viewer. It allows going to the next document in the folder right from the one you’re currently viewing without the need to open it individually. This is especially helpful when viewing hundreds of documents.
- High operating speed. Thanks to the multiple data centers located around the globe, the iDeals’ data transfer speed reaches an industry-leading 200 MBps.
- Industry-leading 99.95% uptime. iDeals guarantees a highly secure and resilient environment with 99.95% uptime.
- Single Sign-On. Enables a single login and password for all projects. Available for Enterprise subscriptions.
- Plugin-free environment. There’s no need to download or install extra software, since iDeals allows viewing protected documents in their native format without plugins.
Document management features
iDeals offers a variety of document security features that aim to keep users’ data confidential and protected:
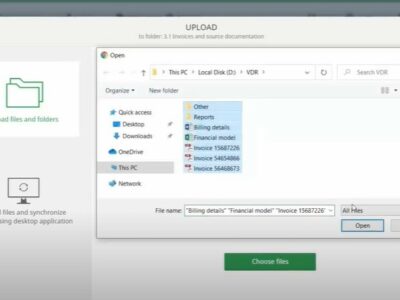
- Drag-n-drop and bulk upload. It enables uploading large volumes of files with a single click.
- Auto indexing. Once uploaded, all files are automatically indexed and numbered in consecutive order.
- File labels. Admins can label files and folders for better document search and categorization.
- Full-text search. Due to the OCR (optical character recognition) technology, it’s easy to find information among hundreds of files using keywords.
- Windows Explorer integration. The iDeals Sync app allows synchronizing files between desktop, FTP, shared folder, or corporate storage and the data room.
- Support of 25+ file formats. The iDeals VDR system can convert 25+ types of files into protected versions for viewing online. However, you can upload files of any type to the data room.
Multi-project management features
iDeals has recently introduce new features tailored to enhance the experience of corporate account administrators:
- Access usage reports. Generate detailed reports that track and analyze how users interact with the data room, including file access and user activity patterns.
- Billing info. Conveniently access and manage all billing information, enabling easy monitoring of subscription details and payment history.
- Invite administrators to any project in your account. Allow for seamless addition of administrators to any project within the account, enhancing collaborative management and oversight.
- Browse all linked projects. Easily view and navigate through all projects linked to the account, providing a comprehensive overview of ongoing activities.
- Browse, search, and delete users [enterprise only]. Efficiently manage users with capabilities to browse, locate specific users through search, and remove users as needed.
- Export usage report & user across projects [enterprise only]. Export comprehensive reports on user activity and resource usage across different projects for in-depth analysis and record-keeping.
- Define server location [enterprise only]. Customize where your data is stored by selecting a preferred server location, enhancing data sovereignty and compliance.
- Customizable room template [enterprise only]. Utilize templates that include preset configurations for security, sign-in processes, and branding, ensuring consistency and ease of setup across projects.
Q&A features
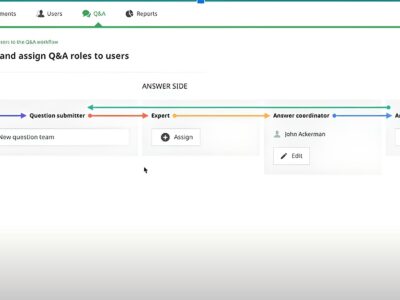
iDeals helps to improve the collaboration within the project thanks to the set of Q&A tools:
- Live discussions. These are protected live forums where virtual data room members can discuss arising issues based on their access permissions.
- Granular access to threads. This feature allows controlling users’ access to confidential discussions by providing granular access to attachments and threads.
- FAQ. It allows for preparing the FAQ list with the most common questions being answered so that users can refer to it while using the virtual data room.
- Full Q&A reports. This feature implies preparing complete reports with all Q&A communication during the project for legal purposes.
- Question statuses. Every question left by virtual data room users receives a status — Answer submitted, Closed, or Reopened. It allows for effective collaboration between parties and saves an admin’s time.
- Expert assignment. When posting a question for an expert in the virtual data room, a user can choose which area it refers to: Finance, Intellectual, Tax, Marketing, or Legal. It significantly speeds up the response.
User management features
It’s easy to manage users within the iDeals virtual data room using the following features:
- 2 permission levels for viewing Excel files. Admins can pick one of the two ways for users to view Excel files — With Formulas or Without Formulas.
- Single/bulk user invitation. It allows inviting users to the virtual data room individually or in groups of thousands equally quickly.
- Invitation customization. It allows customizing the invitation email based on your organization’s look and feel.
- Detailed user roles. Admins can set various levels of access for different users so that they can view or work only with the files they need.
- Mobile device management (MDM). It allows controlling the users’ access to confidential files in the data room on their mobile devices.
- Terms of access. Admins can customize and specify terms of data room access and use, NDAs, and confidentiality agreement.
Reports
Admins can track all the activity inside the virtual data room thanks to the reporting possibilities:
- Page-by-page granular reporting. It allows for identifying what documents were viewed and for how long on a page-by-page basis.
- Custom color-coded reports. It provides color “heat map” reports displaying what files are the most viewed and what groups of users are the most active during the project.
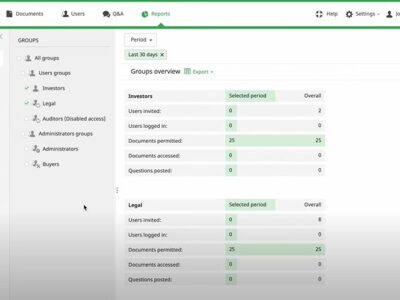
- Group overview reports. It provides insights on the particular group activity: how many users were invited, how many logged in, what documents were accessed, etc.
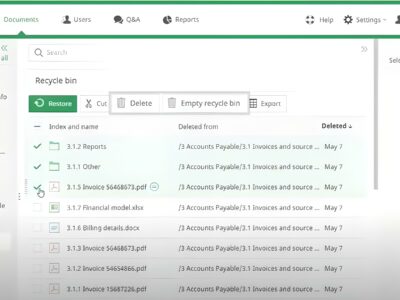
- Full audit trails. Admins can track all the actions taken inside the virtual data room and get complete reports in PDF, Excel, or printed format.
iDeals Integrations
Single Sign-On (SSO)
- iDeals offers SAML 2.0 integration with major providers in the identity management field such as Okta, OneLogin, Ping Identity, Azure AD, and Active Directory Federation Services (AD FS).
AWS Key Management Service (KMS)
It allows for automatically applying an additional encryption key to all data you upload to the project.
Users’ reviews
More Reviews
5 Quick steps to start work with iDeals VDR
1.Sign up to the iDeals virtual data room
1. To start using the iDeals Virtual Data Room tool, you’ll first need to sign up to the service on the product’s webpage. Signing up is easy and your login is protected by two-factor authorization.
2.Decide which documents to upload
2 Depending on what you want this virtual data room solution for, you'll need to make a decision on what documents and files to upload.
3.Organize files and folders
3 If you're planning on doing audits or due diligence in your virtual data room, it's a smart idea to keep your virtual data room organized.
4.Establish user roles and access
4 It will be much easier to specify users' access privileges to the appropriate documents if you organize the files and folders in your VDR. Auditors, for example, can need access to papers that angel investors shouldn't have, and vice versa.
Start working with Top Choice Provider
Go to iDealsLatest news
Leave your review
I recently started using iDeals data room for my M&A projects and I must say, it has been a great experience so far. The interface is incredibly easy to use and the deployment process was a breeze. It’s really helped me to streamline my workflow and make sure that all the important documents are secure and accessible. Highly recommended!
You just know it when you find that perfect data room provider. I’ve tried several, and so far, iDeals is the best one for my needs.
My biggest concern was that my team will struggle to understand a new tool. But with iDeals, the onboarding process went very smoothly. We’re using the data room for occasional due diligence, and no one yet, including our partners, had any problems with understanding the interface.
Real Estate businesses should take a really good look at this data room. We’re using iDeals in our agency, and it makes the workflow so much easier.
We’ve been using iDeals for a couple of months now to manage the work with interns. As a pharmaceutical company, we have a constant flow of interns who need to get access to certain data. iDeals allows us to share files conveniently and safely. Also, it has all the certificates needed for our industry.
We always have a lot of interns who come and go in our company. So we needed a solution that will let us share required information with interns easily and safely. With granular access permissions and time restrictions iDeals works perfectly for our needs. And since we can see all the activities of interns in the data room, it’s easy for us to detect if something is wrong.
We’re using iDeals for fundraising for our social projects. This data room is simple enough for us to never have any issue with it, and for investors to not ask how to use it. We’re working with it for over two years, and I am completely satisfied with it. The interface is intuitive, there are plenty of features, and the data room is secure – what else to wish for?
As a financial services firm, we work with spreadsheets a lot, as you might imagine. So the Fence View feature in the iDeals data room is a lifesaver for us. A lot of my employees have to go to the client’s place to discuss some matters. And this function allows us to keep the information safe in public places.
My friend who also owns a company uses iDeals, so I decided to give it a try. Now I understand why she likes it – the data room is simple and offers every feature I can think of. Moreover, I have to share some very sensitive corporate information from time to time, and iDeals with all its security features seemed to be the only choice. I’m glad I can see the activity of others, it gives me peace of mind.
We tried other data rooms but stopped on iDeals because of the informative and colorful graphs it offers. It’s very convenient for us to use them during board meetings to evaluate the results.
I use this data room to share information with interns in my company, so the opportunity to set the expiration date for their profiles is great for me. I recommend iDeals!
I’m not quite good at technologies, so I looked for the data room that won’t leave my mind twisted. iDeals is perfect because the interface is easy to use, so neither I nor my workers have any issues.
This provider simply justifies its name. iDeals virtual data room is truly ideal! We get all the features we need packed in the neat and easy to work with interface. And the support team is very responsive – they’ve guided us through our first deal so that we can get all the benefits from the data room.
I was using another provider in my company but eventually decided to switch to the iDeals virtual data room. Why? Merely because it is way better than its rivals. The data room is full of useful and unique functions, yet the interface is not overwhelming.
Looking for a data room, we went through numerous providers. Finally, we chose the iDeals virtual data room because of the round-the-clock support and straightforward interface. And the decision was totally right. This provider fulfills all our needs.
Our partners suggested us to try iDeals virtual data room since they’re using it. And we’re thankful for this advice! This provider gives us everything we need to maintain a streamlined exchange of information within the company and beyond it. And the support team was very helpful, guiding us through our first steps.
Our company is using iDeals VDR for three years already, and during this time we only heard that the support team is available 24/7. Because we never had the need to use it. This provider offers the most simple interface ever managing to pack into it all the numerous features. It is a great data room!
We chose iDeals VDR for our company because of the features it has. This data room offers every function you can think of from basic ones like automatic indexing and full-text search to more unique like fence view. There even is a scroll-through viewer that automatically brings the next file after the current one is viewed. This provider is perfect to the details!
While other providers are great only on the paper, iDeals is perfect in real action. This provider helps our company to close deals successfully for more than two years. And even though iDeals VDR was our first experience with data rooms, we would never want to try another provider. A wide set of features, well-thought interface, and the overall sense that you’re taken care of – that’s what iDeals customers get.
As a law firm, we needed some solution that will not just keep the data safe but allow us to work with customers productively. iDeals virtual data room fits our needs just fine, providing us with security features like remote shred and secure spreadsheet viewer. Also, it makes data management very simple. And the interface is easy to use, so our clients don’t have issues with it.
We are absolutely satisfied with this provider. iDeals VDR has every function we need – watermarks, fence view, integration with Windows Explorer, and many others. We’ve tried several different providers before this one, and iDeals is merely the best one.